Apr 26, 2023
Array
.png)
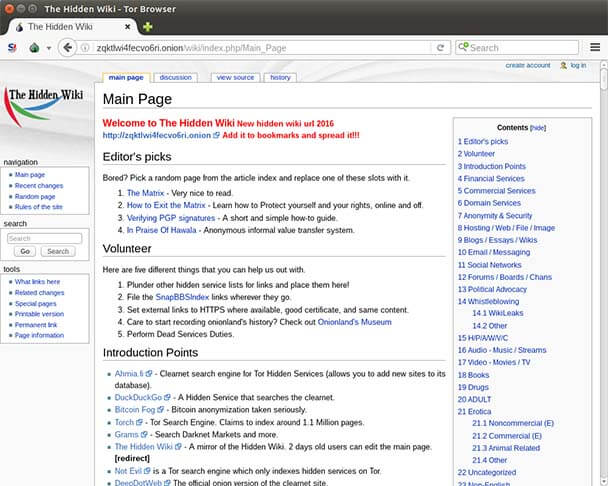
One effective technique for enhancing your online privacy when browsing the Dark Web is called Tor over VPN. This method provides an added layer of protection compared to using Tor alone. A recent article titled "Improved Security for Tor Users" recommends this approach. It's important to note that not all Dark Web search engines are secure. While Ahmia is a popular option, it operates differently from traditional search engines and takes additional measures to ensure user safety.
Dark web onions are often associated with illegal activities, but in reality, most people who get caught using Tor for illicit purposes are traced through other means. To increase your privacy and security, it's recommended to connect to a VPN before using Tor, also known as Tor over VPN. This method not only offers the anonymity of the Tor network but also adds an extra layer of protection that prevents any Tor node from accessing your home IP address.
The Secret World of Alpha Market: A Journey into the Dark Web Onions
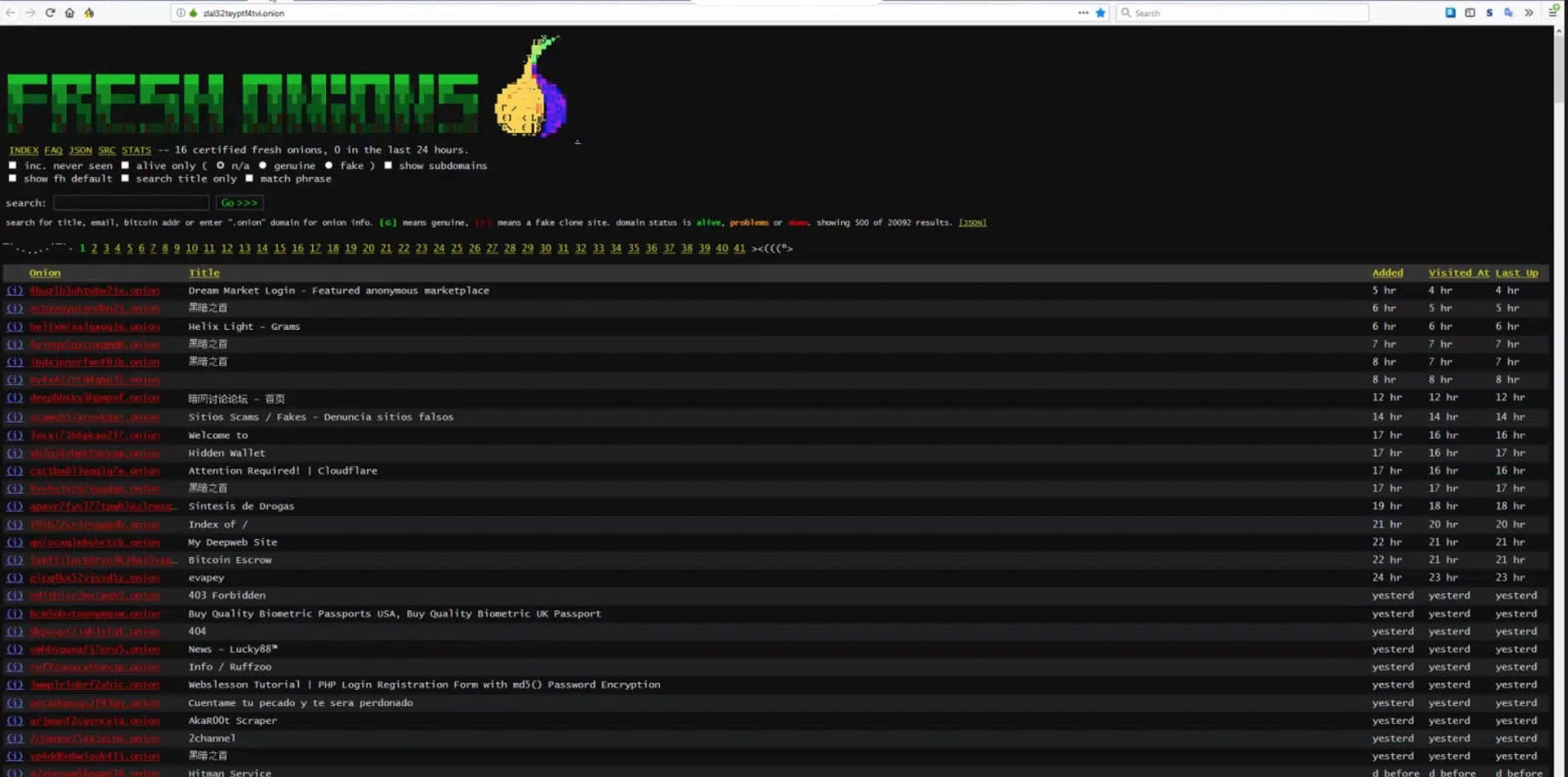
Dark web onions are notorious for being difficult to access and navigate. These websites are only accessible through the use of specialized software, such as Tor, which allows users to browse the internet anonymously. However, even with Tor, finding the right onion site can be a challenge, especially since the site location can change frequently due to reported outages. It's crucial for users to exercise caution and discretion when accessing these sites, as they often host illegal activities and content. As technology advances, the dark web continues to evolve, making it increasingly difficult for authorities to track and shut down these illicit operations.
Instead of relying on traditional search engines, it's recommended to use DuckDuckGo - one of the more reliable search engines on the dark web - to locate the content you seek.
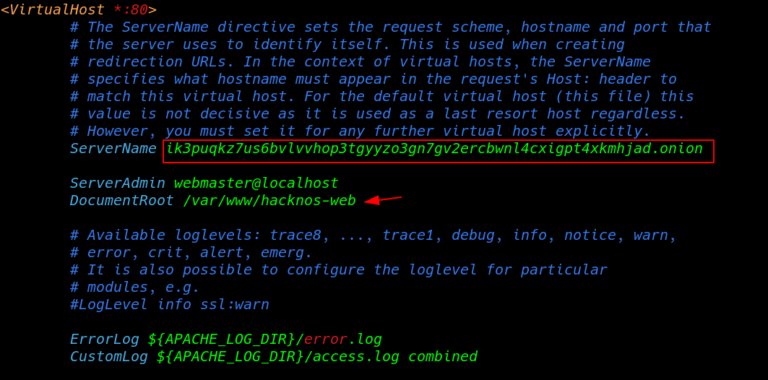
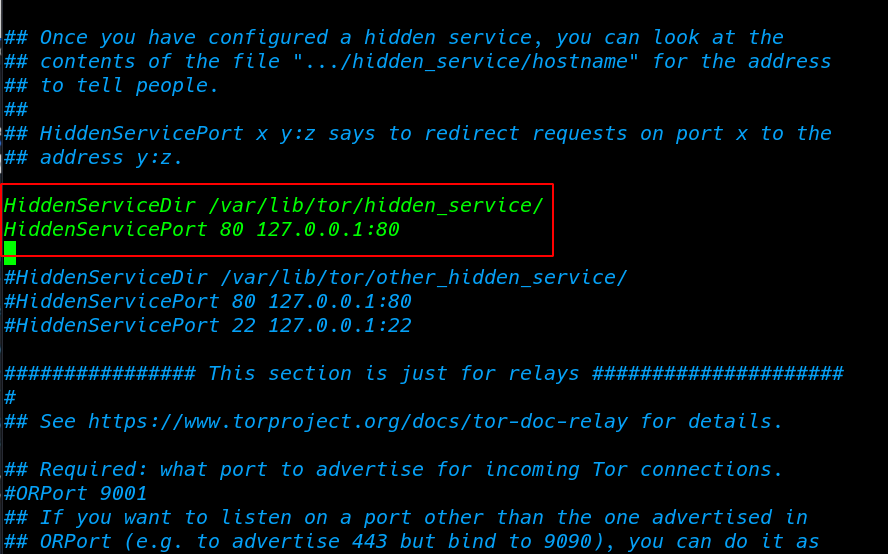
The Hidden Wiki is an excellent starting point for exploring the dark web, specifically for dark web onions. These onions are hosted on web servers just like any other site, but the server configuration is altered to only respond to the localhost. With this configuration, users can access the site without revealing their IP address or location. Muffett, Alec.
Inside the Shadowy World of Alphabay Market on the Dark Web
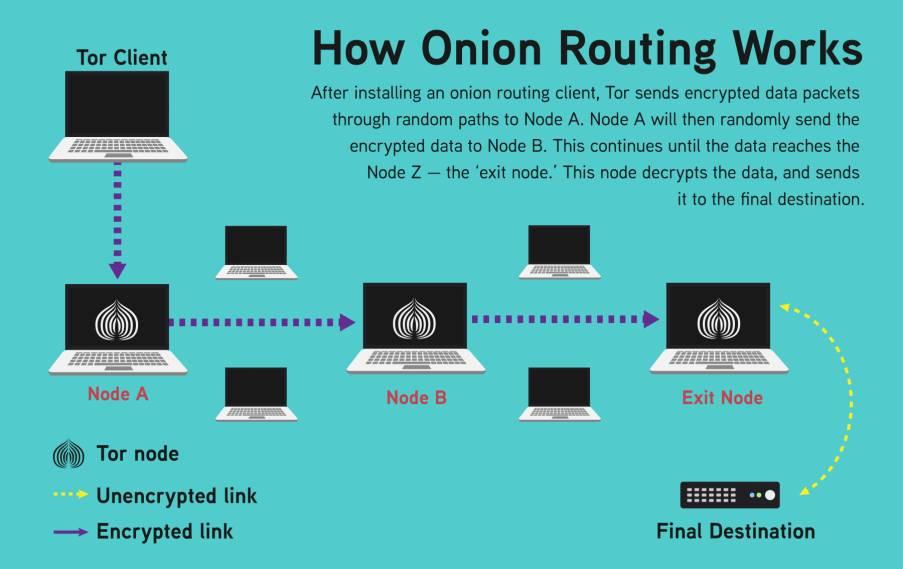
Dark web onions have become a popular destination for those seeking anonymity and privacy online. These websites, which can only be accessed through the Tor network, allow users to browse and communicate without revealing their identity or location. Unlike traditional websites, dark web onions are not indexed by search engines and their URLs are composed of random characters, making them difficult to find. When accessing a dark web onion, your traffic is bounced through multiple servers before reaching its destination, adding an extra layer of security and privacy. While the dark web is often associated with illegal activities, there are also legitimate uses for this hidden network, such as journalism and whistleblowing.
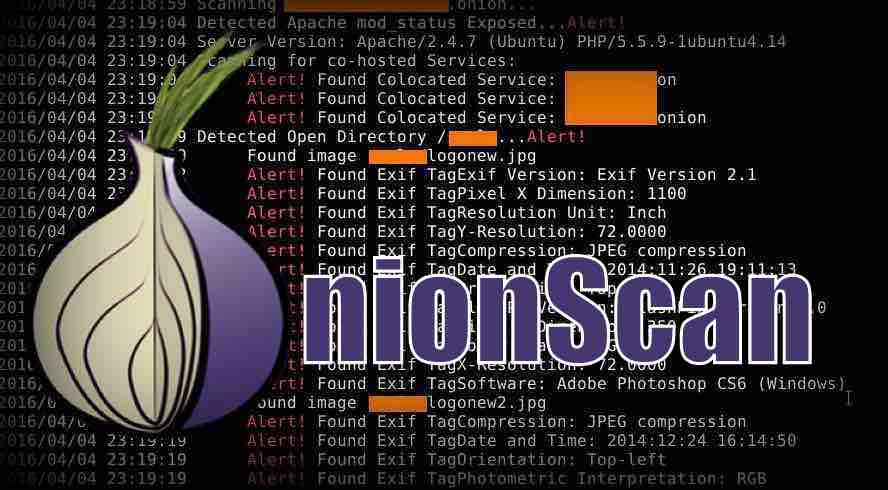
Dark web onions are a fascinating topic for those interested in privacy and anonymity. When accessing the dark web, the exit node is aware of the site you are connecting to, but not your identity. However, this feature is disabled by default in the -alpha version due to the potential for application-level attacks. The 3-series Tor, which was once considered "stable," is now obsolete. If you're looking to protect your privacy on the dark web, PrivacyTools offers a vast directory of anti-surveillance tools, services, and educational resources. Utilizing a VPN server before launching the Tor Browser can also help hide your IP address from any node in the Tor network and conceal the fact that you're using Tor from your network operator.
"Advantages of Using TOR2WEB-Proxy for Dark Web Onions". This information was retrieved by Willis on September 10, 2015. The funding for TOR2WEB-Proxy comes from the Sandler Foundation's deep pockets and other similar organizations.
When it comes to the dark web, onions are a crucial part of the network. However, the Tor Rendezvous Specification poses a threat to both the gateway and the service. With the ability to fingerprint the browser, it becomes easier to access user IP address data, which raises concerns for privacy and security.
Secrets of the Dark Web: Alphabay Market and the Darknet Onions
You cannot access dark web onion sites through your regular web browser, the one you are likely using to view this page. It is important to also avoid various spin-off sites with similar names. As a result, the dark web has become a hotbed for illegal activities.
The dark web is home to a plethora of hidden websites, including those that are accessible only through onion addresses. These sites can be a source of valuable information, but users should be cautious as there are many unregulated and dangerous activities taking place on the dark web. It's important to note that accessing copyrighted material through sites like Sci-Hub is illegal and banned in several countries, so users should exercise caution when browsing the dark web.
Have you ever stumbled upon the term ".onion" while browsing the internet? If you have, chances are you were exploring the dark web. But why is it that you can't access.onion sites like regular websites?
Well,.onion is actually a special top-level domain suffix that is used for anonymous and hidden services on the Tor network. Tor (The Onion Router) is a free and open-source software that allows users to browse the internet anonymously by bouncing their connection through a network of relays.
.onion sites are not indexed by search engines and can only be accessed through the Tor browser. This is because they are designed to be hidden and anonymous, allowing users to communicate and access information without revealing their identity or location.
So, while you may not be able to access.onion sites like regular websites, they serve an important purpose for those who require anonymity and privacy online.
Explore further
Distributed by XTJ7, LLC.